Latest Security News
-
Critical Everest Forms Pro flaw exploited to take over WordPress sites
-
Hackers are actively exploiting a critical vulnerability (CVE-2026-3300) in
the Everest Forms Pro plugin, which lets them take complete control of a
WordPr...
18 hours ago
-
Viruses With Wings and Brains: The Worm You Cannot Patch
-
Viruses With Wings and Brains: The Worm You Cannot Patch
// elusive thoughts // malware // ai security
Gary McGraw gave this whole problem the only label ...
1 day ago
-
Elon Musk’s XChat: how secure is the new messaging app? | Kaspersky
official blog
-
Breaking down Elon Musk’s XChat: how its end-to-end encryption works, why
experts have slammed its PIN system, and how the new service stacks up
against Si...
1 day ago
-
AI Worm
-
Researchers have prototyped an AI-powered internet worm.
The coolest thing about the prototype is that it carries its own LLM with
it, and runs it on com...
1 day ago
-
Hackers Used Meta’s AI Support Bot to Seize Instagram Accounts
-
The Instagram accounts for the Obama White House and the Chief Master
Sergeant of the U.S. Space Force were briefly defaced with pro-Iranian
images and mes...
5 days ago
-
Overview of Content Published in May
-
Here is an overview of content I published in May: Blog posts: Update:
search-for-compression.py Version 0.0.7 SANS ISC Diary entries: Wireshark
4.6.5 Rele...
6 days ago
-
הגליון המאה שמונים ושישה של DigitalWhisper שוחרר!
-
הגליון המאה שמונים ושישה של DigitalWhisper שוחרר!פורסם ב- May 31, 2026
21:11:09, על ידי- sapirxfed
ברוכים הבאים לדברי הפתיחה של הגליון ה-186 של DigitalWh...
6 days ago
-
CVE-2026-0257: Rapid7 Caught Attackers Abusing Forged VPN Cookies Against
Multiple Customers
-
CVE-2026-0257 lets attackers forge Palo Alto GlobalProtect auth cookies and
bypass VPN login. Exploitation confirmed since May 17. Palo Alto Networks
addre...
6 days ago
-
Domain Exploit Detector
-
Dear blog readers,
This is Dancho.
I recently launched my commercial Domain Exploit Detector service and I
also published it on Github including several ...
2 weeks ago
-
Mandiant Global Median Dwell Time Deteriorates from 11 to 14 Days
-
Oh snap. My single most important cybersecurity metric deteriorated again.
In the M-Trends report for calendar year 2024, Mandiant’s global median
dwe...
2 months ago
-
Recommended: MCP Is Broken and Anthropic Just Admitted It
-
I recommended MCP Is Broken and Anthropic Just Admitted It on TysonRhame.
About me: http://www.chuvakin.org
5 months ago
-
BestAV (Fake Antispyware affiliate) exposed
-
Hello everyone, it's been a while.
One of the first affiliate systems I ever infiltrated was BestAV, back in
2011, the same year I started XyliBox.
Over...
8 months ago
-
רעיון לשיפור אבטחת SSL VPN – צמצום משטח התקיפה של ה-Gateway על ידי מתן גישה
רק ללקוחות DDNS שאושרו מראש
-
(שלום רב קוראים יקרים – אם אתם מכירים מישהו שעובד עבור יצרנית של SSL VPN –
בפיתוח תוכנה, ניהול מוצר וכדומה, אנא שלחו לו או לה קישור לפוסט הזה, בתקווה
שהר...
9 months ago
-
Readying hospital defenses for the AI-powered phishing surge
-
Artificial Intelligence
Privacy & Security
Workforce
As phishing tactics evolve, healthcare organizations need to act quickly to
shore up defenses and close...
10 months ago
-
How Security and Privacy Teams Break Barriers Together
-
While cybersecurity and data privacy leaders have distinct expertise, our
fundamental goals are aligned. By understanding each other’s perspectives
and pri...
11 months ago
-
Shodan-Dorks - Dorks for Shodan; a powerful tool used to search for
Internet-connected devices
-
This GitHub repository provides a range of search queries, known as
"dorks," for Shodan, a powerful tool used to search for Internet-connected
devices. T...
1 year ago
-
Andrew Hay’s 2025 Cybersecurity Predictions
-
As we approach 2025, the ever-evolving landscape of cybersecurity continues
to challenge professionals and organizations alike. Based on observed
trends an...
1 year ago
-
North Korean hackers posing as IT workers steal over $1B in cyberattack
-
North Korean hackers posing as IT workers steal over $1B in cyberattack
l33tdawg Fri, 11/29/2024 - 10:31
1 year ago
-
Eye care company suffers 377K-record data breach
-
Panorama Eyecare, a Fort… read more
1 year ago
-
-
What a lovely sunset
-
Oh, hi. Long time no blog, eh?
Well, it is time to sunset this blog, I will be deleting it in the next few
weeks.
So long, and thanks for all the fis...
3 years ago
-
Simple PHP webshell with php filter chains
-
Recently found an LFI in a PHP application and one of the cool things I
learned about recently was PHP filter chains. More info here:
https://www.synacktiv...
3 years ago
-
A Scam in the Family—How a Close Relative Lost $100,000 to an Elder Scam
-
Written by James Schmidt Editor’s Note: We often speak of online scams in
our blogs, ones that cost victims hundreds...
The post A Scam in the Family—Ho...
3 years ago
-
Symantec Identity: Stepping Up to Meet the COVID-19 Crisis
-
COVID-19 confronted healthcare providers and governments with unprecedented
requests for access, aid, and assistance. Here’s how one team at Symantec
is ri...
6 years ago
-
Getting DNS Client Cached Entries with CIM/WMI
-
What is DNS Cache The DNS cache maintains a database of recent DNS
resolution in memory. This allows for faster resolution of hosts that have
been queried ...
6 years ago
-
How Reverse Engineering (and Cyber-Criminals’ Mistakes) Can Help You When
You’ve Been a Ransomware Victim
-
Ransomware is a type of malware that threatens to publish the victim’s data
or perpetually block access to it unless a ransom is paid. In the last two
year...
6 years ago
-
-
Random CSO Musing
-
One of the biggest challenges of running a security organization is
balancing the ongoing efforts, with strategic directions, all while keeping
the “pressu...
7 years ago
-
Lucky Break
-
One of the things I do from time to time is throw out an open ended
question on Twitter. Sometimes I’m making a point, sometimes I just want
to amuse myse...
7 years ago
-
Indonesian Spam Communities
-
In our last post we tried to shed some light at what seemed to appear as a
very common PayPal phishing email at first glance, but evidently turned out
to b...
7 years ago
-
TekThing 161 – Bitcoin Sucks For Gaming PCs!!! Our Video Gear, Fingbox Home
Network Security
-
—— Thank You Patrons! Without your support via patreon.com/tekthing, we
wouldn’t be able to make the show for you every week!
https://www.patreon.com/tekth...
8 years ago
-
Romania is vice-champion at the European Cyber Security
-
CERT-RO The National Response Center for Cyber Security Incidents affirmed
on Friday that Romania, for the second consecutive year, has become the
European...
8 years ago
-
CoalaBot : http Ddos Bot
-
CoalaBot appears to be build on August Stealer code (Panel and Traffic are
really alike)
I found it spread as a tasks in a Betabot and in an Andromeda sp...
8 years ago
-
Social-Engineer Toolkit (SET) v7.7 “Blackout” Released
-
TrustedSec is proud to announce a major release of the Social-Engineer
Toolkit (SET) v7.7. This version incorporates support for hostnames in the
HTA att...
8 years ago
-
Big Changes Around the Corner for the IoT
-
The IoT is transforming before our eyes due to increasing regulations,
growing demand for security standards and advancements in the telecom
industry.
T...
9 years ago
-
ClearEnergy ransomware can destroy process automation logics in critical
infrastructure, SCADA and industrial control systems.
-
Schneider Electric, Allen-Bradley, General Electric (GE) and more vendors
are vulnerable to ClearEnergy ransomware. Researchers at CRITIFENCE®
Critical I...
9 years ago
-
ROOTCON 10 Capture The Flag Statistics
-
During ROOTCON 10, we introduced a new dedicated track for our Capture The
Flag, with the comfortable CTF tables and chairs the game was well
participated ...
9 years ago
-
קיר הבושה: מחצית ראשונה של שנת 2016 - מגמות בפגיעה במידע רפואי בארה"ב
-
תרגום מאמר :
http://www.healthcareinfosecurity.com/wall-shame-mid-year-2016-breach-trends-a-9245
שני דברים שאני, יאיר, לוקח מהמאמר הזה כלקחים נכון להיום:1....
9 years ago
-
The ‘Compliance Only / CISSP / Minimum Viable Product / HR firewall’
infosec trapezoid of fuck
-
Yesterday (thurs, 3/24/16) I went on a tirade on twitter, regarding an
experience I had in San Francisco during RSA week, while at a vendor party.
I’ll let...
10 years ago
-
Dridex Down Under
-
Raytheon | Websense® Security Labs™ has been tracking malicious email
campaigns associated with the Dridex banking Trojan since 2014. An
interesting deve...
10 years ago
-
[Updated] Nurturing JavaScript Obfuscation and Fast Flux DNS - "Whats App
Voicemail Spamming" for Russian Online Pharmacies!
-
Recently, we analyzed that spammers are doing "Whats App Fake Voicemail"
spamming to trick end-users to visit online pharmacies' websites. There are
high...
10 years ago
-
What Verizon Missed in the Latest Threat Reports
-
* By: Zuk Avraham, Joshua Drake, Yaniv Karta, Jimmy Sha *
* Read the full report - here Recently, Veriz...
10 years ago
-
Forensic
-
אחת מהבעיות העיקריות בביצוע תהליך FORENSIC הוא לאחר ביצוע תהליך שיכפול ה -
Harddisk (על פי כל התקנים של שיכפול ביט אחרי ביט), היא לבצע מחקר על *מחשב
חי...
11 years ago
-
Blog Moved
-
Please see the Trustwave SpiderLabs Blog.
11 years ago
-
TrustKeeper Scan Engine Update – February 4, 2015
-
The latest update to the TrustKeeper scan engine that powers our Trustwave
Vulnerability Management product (including both internal and external
vulnerabi...
11 years ago
-
RSA Announces End of RSA Security Conference
-
Aims to bring clarity to cloudy marketing messages through exhibit hall
chotskies Bedford, MA., – April 1, 2014 – RSA, the security division of
EMC, today ...
12 years ago
-
botCloud – an emerging platform for cyber-attacks
-
Hosting network services on Cloud platforms is getting more and more
popular. It is not in the scope of this article to elaborate the advantage
of using Cl...
13 years ago
-
mimikatz: Tool To Recover Cleartext Passwords From Lsass
-
I meant to blog about this a while ago, but never got round to it. Here’s a
brief post about very cool feature of a tool called mimikatz. I’m very
grateful...
14 years ago
-
Pentestify.
-
i’m over here now.
14 years ago
-
-
-
-
-
-
-
-
-
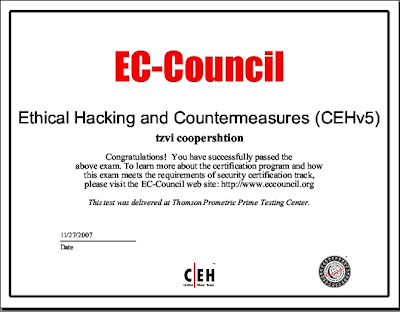
Got my CEH certification!