taken from SANS internet storm center :
Introduction
Security Operation Center (SOC) analysts investigate alerts on suspicious network activity. However, these analysts might not run across exploit kit (EK) traffic that often. An organization's web gateway can stop a great deal of bad traffic before you see a full infection chain. Investigating other types of suspicious activity will likely take up the majority of an analyst's workday.
Some of us are lucky enough to review EK traffic on a routine basis. What that in mind, I want to share examples of the most common exploit kits I've noticed so far this year.
In order, the EK traffic I've seen most often in 2015 has been:
- Angler
- Fiesta
- Nuclear
- Neutrino
- Magnitude
- Rig
This isn't a comprehensive list. Other exploit kits are out there, but these are most common that I've seen this year. I don't have any hard numbers, and the last four (Nuclear, Neutrino, Magnitude, and Rig) are more of an educated guess for the ranking. The EK scene can evolve fairly quick. The list will likely change within a few months, and my observations are only one person's view.
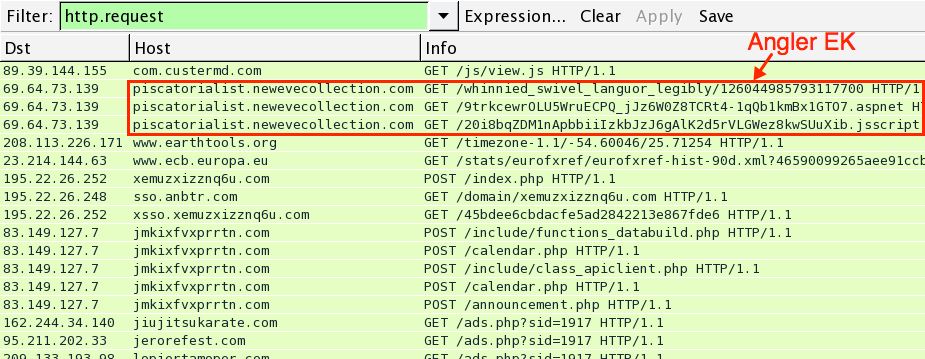
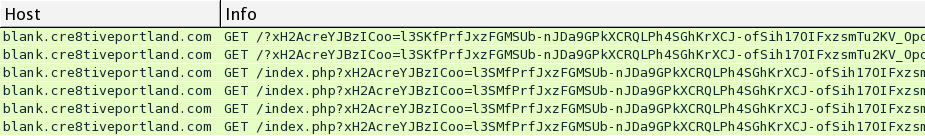
Angler EK
Angler is the most common exploit kit I run across. It's also the most advanced. Angler changes URL patterns frequently, and these changes have recently happened on a near-daily basis. Angler started using "fileless" infection techniques in 2014 [1], and it now sends its payload in a fairly sophisticated encrypted manner (meaning it doesn't use a straight-forward ASCII string to XOR the payload when it's sent over HTTP). In recent months, I've had a hard time obtaining the payload from Angler EK. In the example for this diary, I wasn't able to obtain or decrypt the payload.
Previously, I've seen Angler sending some form of ransomware like the TeslaCrypt/Alpha Crypt variants [2] or CrytoWall 3.0 [3]. In the past few days, I've mainly seen Bedep and related payloads sent by Angler.
- An example of Angler EK traffic on 2015-06-03: click here for the pcap file.
Fiesta EK
Fiesta is probably the next-most common exploit kit I've run across, most of it related to the BizCN actor that I described in a previous diary [4]. Other actors certainly use this exploit kit. Like Angler EK, Fiesta also uses a more sophisticated type of encryption when sending the malware payload. Fortunately, I can usually grab a copy of the payload from an infected host in my lab or decrypt the payload when necessary.
- Example 1 of Fiesta EK traffic on 2015-06-03: click here for the pcap file.
- Example 2 of Fiesta EK traffic on 2015-06-03: click here for the pcap file.
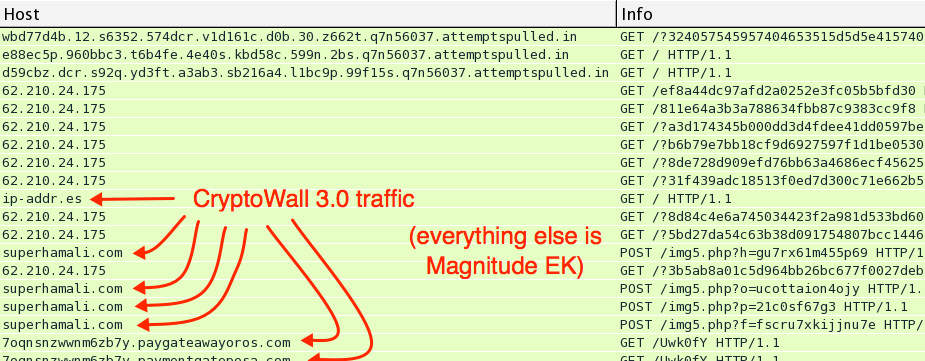
Magnitude EK
Magnitude EK often sends several payloads, sometimes 6 or more. It's a very noisy exploit kit. I'll often see CryptoWall 3.0 as one of the payloads. In the example for this diary, Magnitude only sent one payload, and that was CryptoWall 3.0. I've usually seen Magnitude EK send the malware payloads unencrypted, at least when using IE 8 as a web browser in the vulnerable host. I don't see Magnitude now as much as I did last year.
- An example of Magnitude EK traffic on 2015-06-03: click here for the pcap file.
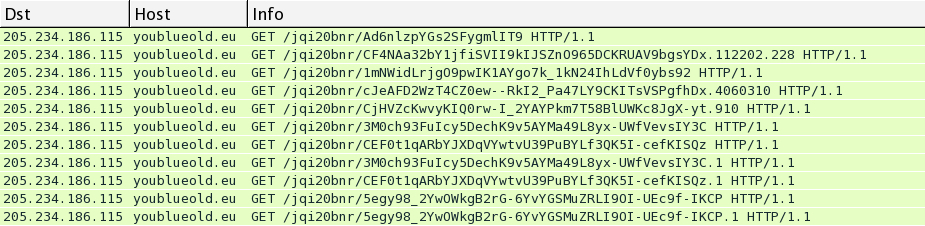
Neutrino EK
In 2014, this exploit kit disappeared for about six months then came back in a much different form [5]. Traffic patterns have remained relatively unchanged since it reappeared in late 2014. Neutrino EK uses a more sophisticated style of encryption when sending the malware payload (not merely a straight-forward XOR using an ASCII string).
Neutrino's current URL patterns remind people of Sweet Orange EK; however, Sweet Orange seems to have disappeared from the scene back in February of 2015. I haven't found any Sweet Orange after February, but I've seen plenty of Neutrino since then. If you see recent traffic you think is Sweet Orange, double check it. It's probably Neutrino EK.
Neutrino has been relatively consistent over the past few months. Haven't seen a lot of it, but it's never gone away.
- An example of Neutrino EK traffic on 2015-06-03: click here for the pcap file.
Nuclear EK
Last year, this exploit kit seemed much more common than it is today. Operation Windigo still uses Nuclear EK [6], but in recent weeks, I've rarely seen Nuclear outside of that. Nuclear EK obfuscates its payload by XOR-ing it with an ASCII string.
- An example of Nuclear EK traffic on 2015-06-03: click here for the pcap file.
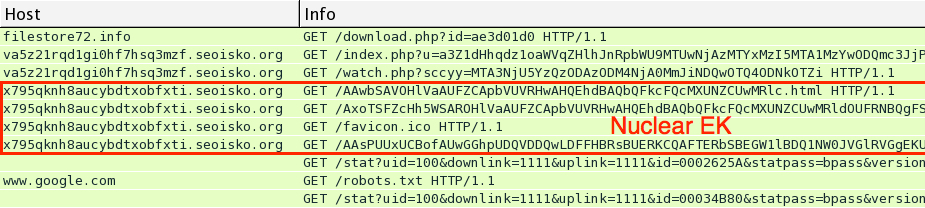
Shown above: Nuclear EK traffic and post-infection activity associated with Operation Windigo on Wednesday 2015-06-03.
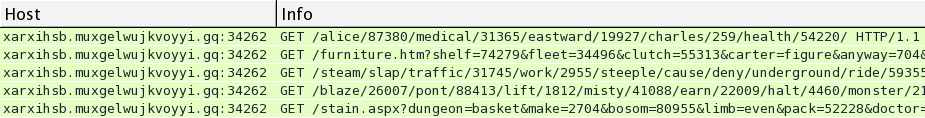
Rig EK
When Rig first appeared in 2014, it looked remarkably similar to Infinity EK [7] (which was first identified as Goon EK). Rig EK apparently borrowed a great deal from Infinity. While I haven't seen Infinity this year, I've definitely run across Rig every once in a while.
In April 2015, Rig EK changed the encryption it uses for sending the malware payload. Now, it uses the same method as Nuclear EK, obfuscating its payload by XOR-ing it with an ASCII string [8].
- An example of Rig EK traffic on 2015-06-03: click here for the pcap file.
Final words
As mentioned earlier, this is merely one person's view into the current state of exploit kits. It's not comprehensive, and there are other exploit kits I don't have visibility on. Here's a list of pcap files from the previous paragraphs:
- http://malware-traffic-analysis.net/2015/06/03/2015-06-03-Angler-EK-traffic.pcap
- http://malware-traffic-analysis.net/2015/06/03/2015-06-03-Fiesta-EK-traffic-example-01.pcap
- http://malware-traffic-analysis.net/2015/06/03/2015-06-03-Fiesta-EK-traffic-example-02.pcap
- http://malware-traffic-analysis.net/2015/06/03/2015-06-03-Magnitude-EK-traffic.pcap
- http://malware-traffic-analysis.net/2015/06/03/2015-06-03-Neutrino-EK-traffic.pcap
- http://malware-traffic-analysis.net/2015/06/03/2015-06-03-Nuclear-EK-traffic-Operation-Windigo.pcap
- http://malware-traffic-analysis.net/2015/06/03/2015-06-03-Rig-EK-traffic.pcap
I've also collected the exploits and malware payloads where I could. A zip file with this collection is available at:
The zip file is password-protected with the standard password. If you don't know it, email admin@malware-traffic-analysis.net and ask.
---
Brad Duncan
ISC Handler and Security Researcher at Rackspace
Blog: www.malware-traffic-analysis.net - Twitter: @malware_traffic
Brad Duncan
ISC Handler and Security Researcher at Rackspace
Blog: www.malware-traffic-analysis.net - Twitter: @malware_traffic
References:
[1] http://malware.dontneedcoffee.com/2014/08/angler-ek-now-capable-of-fileless.html
[2] https://isc.sans.edu/diary/Angler+exploit+kit+pushes+new+variant+of+ransomware/19681
[3] https://isc.sans.edu/diary/Angler+exploit+kit+pushing+CryptoWall+30/19737
[4] https://isc.sans.edu/diary/Actor+using+Fiesta+exploit+kit/19631
[5] https://isc.sans.edu/diary/Exploit+Kit+Evolution+Neutrino/19283
[6] http://www.rackspace.com/blog/in-2015-operation-windigo-is-still-going-strong/
[7] http://www.kahusecurity.com/2014/rig-exploit-pack/
[8] http://malware-traffic-analysis.net/2015/05/06/index2.html
[2] https://isc.sans.edu/diary/Angler+exploit+kit+pushes+new+variant+of+ransomware/19681
[3] https://isc.sans.edu/diary/Angler+exploit+kit+pushing+CryptoWall+30/19737
[4] https://isc.sans.edu/diary/Actor+using+Fiesta+exploit+kit/19631
[5] https://isc.sans.edu/diary/Exploit+Kit+Evolution+Neutrino/19283
[6] http://www.rackspace.com/blog/in-2015-operation-windigo-is-still-going-strong/
[7] http://www.kahusecurity.com/2014/rig-exploit-pack/
[8] http://malware-traffic-analysis.net/2015/05/06/index2.html